Testing OAuth and JWT Authentication Systems
Ten years ago, web authentication was relatively straightforward. A user typed their username and password into a website, the server checked the database, and if the credentials matched, the server created a stateful "Session Cookie" in its memory. For modern microservices, single-page applications (SPAs), and mobile apps, this stateful model is fundamentally broken. It simply cannot scale.
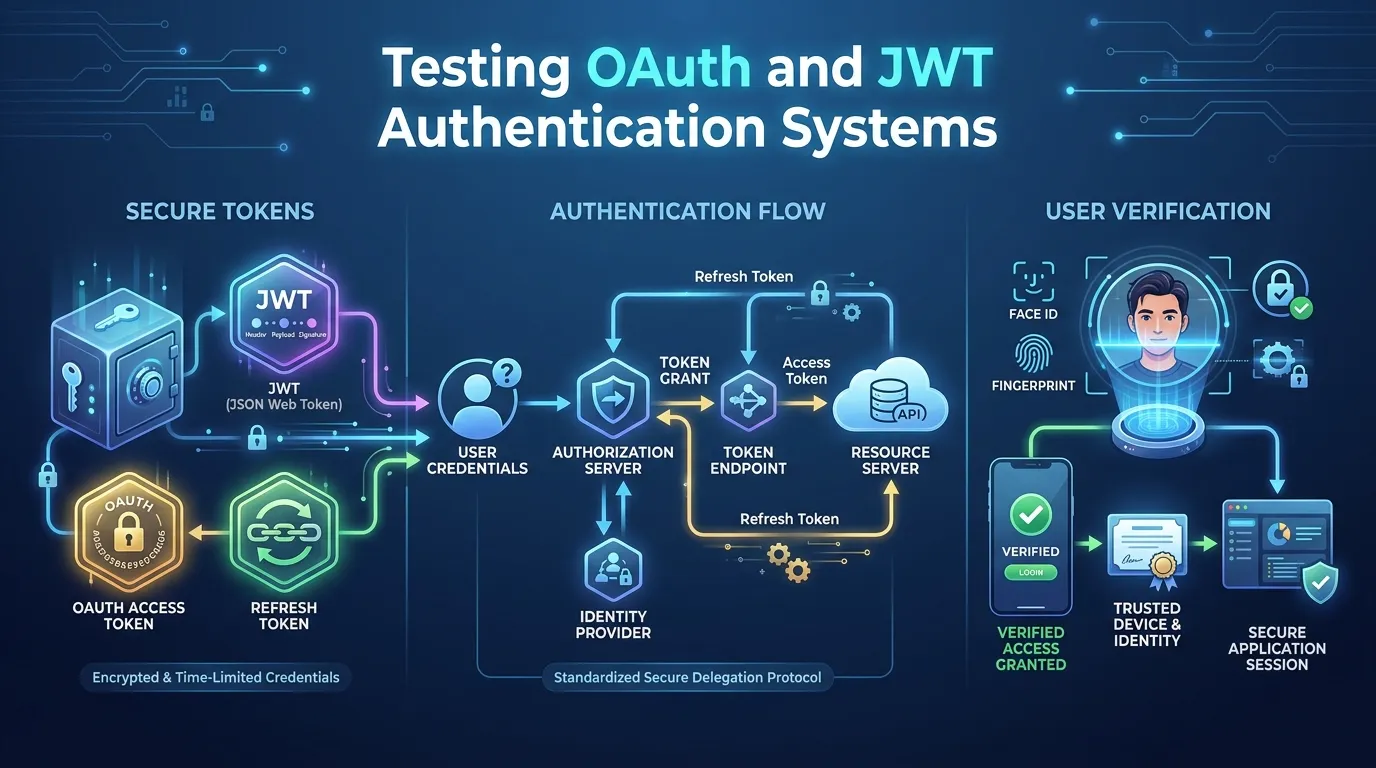
To solve the scaling crisis, the industry rapidly adopted stateless authentication models, primarily driven by the OAuth 2.0 authorization framework and JSON Web Tokens (JWTs). While these technologies brilliantly solve the problem of distributed scale, they introduce massive cryptographic complexity. If improperly implemented, an attacker can silently forge their own administrative tokens and bypass the entire login screen entirely. In this hyper-technical 2026 guide, we will dissect the mechanics of modern tokens and explore advanced methodologies for OAuth JWT testing to prevent catastrophic authentication bypasses.
The Mechanics of Modern Authentication
Before testing the flaws, you must understand the architecture. Modern identity relies on a separation of concerns: Authentication (OpenID Connect), Authorization (OAuth 2.0), and the physical token format (JWT).
How OAuth 2.0 Works
OAuth 2.0 is an authorization framework. It allows an application to obtain limited access to a user's account on an HTTP service. Think of a hotel keycard. When you check into a hotel (Authentication), the clerk verifies your ID. They then hand you a generic plastic keycard (the OAuth Token). The keycard does not know your name or your social security number. It only contains cryptographic permission: "Allow access to Room 402 for exactly 3 Days." You hand that keycard to the door lock; the door doesn't care who you are, it only checks if the signature on the card is mathematically valid.
The Anatomy of a JWT
A JSON Web Token (JWT) is the standard format for that plastic hotel keycard. It consists of three Base64Url-encoded strings, separated by dots: Header.Payload.Signature.
- Header: Identifies the cryptography used (e.g.,
{"alg": "RS256"}). - Payload (Claims): The actual permissions (e.g.,
{"user_id": 123, "role": "admin", "exp": 1712345678}). - Signature: The cryptographic math proving the token was genuinely created by the server and hasn't been altered by an attacker.
Testing the OAuth Authorization Flow
Testing OAuth requires validating the intricate "dance" between the Client, the Authorization Server, and the Resource Server.
PKCE Validation (Proof Key for Code Exchange)
In modern implementations (especially for mobile apps and SPAs), the "Authorization Code Code Flow with PKCE" is mandatory.
The Test: During the OAuth flow, the client app generates a random secret (code_verifier) and sends a hashed version of it (code_challenge) to the server. Later, the client must send the original code_verifier to get the final JWT.
A penetration tester will attempt an "Authorization Code Interception" attack. They will steal an authorization code from the network and attempt to exchange it for a token without providing the correct code_verifier. If the server hands over the JWT anyway, the PKCE implementation is broken and vulnerable to token theft.
Redirect URI Manipulation
When you click "Login with Google," Google eventually redirects you back to your application with the authorization code.
The Test: The tester intercepts the original login request and modifies the redirect_uri parameter to point to the attacker's evil server (e.g., redirect_uri=https://evil-server.com). If the Authorization server is misconfigured (e.g., it allows wildcard matching like *.yourcompany.com), it will gladly send the user's secret code directly to the attacker, leading to total account takeover. Strict, byte-for-byte URI matching is the only secure defense.
Exploiting JWTs: Algorithm Confusion and 'None' Attacks
The vast majority of authentication bypasses occur not in the OAuth flow, but in the server's failure to properly validate the cryptographic math of the JWT signature.
The "None" Algorithm Attack
The JWT header dictates the algorithm in the "alg" field. Unbelievably, the JWT specification officially includes an algorithm called "none".
The Test: A tester logs in as a basic user and receives their valid JWT. They decode the token, modify the payload to say "role": "admin", change the header to say "alg": "none", delete the cryptographic signature from the bottom of the token, and send it to the server.
If the backend application is using an outdated or misconfigured JWT library, it will read "alg": "none", conclude that "no signature is required," and grant the attacker full administrative access. Advanced OAuth JWT testing tools instantly check every endpoint for this exact vulnerability.
Algorithm Confusion (Asymmetric to Symmetric)
This is a more complex cryptographic attack. Servers often use Asymmetric encryption (RS256) to sign tokens. This involves a Private Key (kept secret on the server to sign the token) and a Public Key (freely available to anyone to verify the signature).
The Test: The attacker downloads the server's Public Key. They forge a malicious admin token. But instead of signing it with RS256, they change the header to HS256 (Symmetric encryption, where the same key is used to both sign and verify). They then sign the forged token using the Public Key as the secret passphrase.
If the server is misconfigured, it will see HS256, grab its Public Key (thinking it's grabbing the shared symmetric secret), run the math, and validate the attacker's forged token perfectly.
Validating the JWKS (JSON Web Key Set) Endpoint
To support key-rotation and distributed verification, modern identity platforms (like Okta or Auth0) host a public endpoint called a JWKS URI (e.g., https://your-domain.com/.well-known/jwks.json). This JSON file contains the public keys necessary to verify the JWTs.
Testing the security of the JWKS implementation is critical:
- The Injection Test: A JWT header can contain a
jku(JWK Set URL) parameter, instructing the server where to fetch the public keys. A tester will create a forged token and point thejkuparameter tohttps://evil-hacker.com/jwks.json. If the server blindly trusts this header, it will download the attacker's public key, validate the attacker's forged signature, and grant administrative access. Testing must verify that the server only acceptsjkuaddresses from a strict, immutable whitelist.
Defending Against Token Hijacking
Even perfect cryptography is useless if the token itself is stolen. Because the server is stateless, a valid JWT is equivalent to cash; whoever holds the JWT controls the account.
The Storage Dilemma
A massive portion of JWT testing revolves around examining the frontend application (React, Angular).
If the frontend stores the JWT in localStorage or sessionStorage, it is entirely vulnerable to Cross-Site Scripting (XSS). An attacker can inject a tiny JavaScript payload that reads localStorage.getItem('token') and silently uploads the JWT to their hacker server.
The Fix/Test: Testing must enforce that tokens are stored in HttpOnly, Secure cookies. JavaScript absolutely cannot read an HttpOnly cookie, rendering XSS token theft impossible.
Token Binding (DPoP)
In 2026, the cutting edge of token security is Demonstration of Proof-of-Possession (DPoP). Without DPoP, a JWT is a "Bearer Token"—whoever bears it, wields the power. With DPoP, the token is cryptographically bound to the specific web browser that requested it. If a Russian attacker steals the American user's DPoP-enabled JWT and attempts to use it from their own laptop, the server will instantly reject the token because the attacker cannot provide the mathematical proof that they possess the American user's specific browser session.
Step-by-Step: Auditing a JWT Implementation
Testing JWTs requires a structured, manual approach. Automated scanners often miss subtle cryptographical logic flaws.
Step 1: Capture and Decode
Use an intercepting proxy (like Burp Suite) to capture the login request. Copy the Base64 JWT and decode the Header and Payload using a tool like jwt.io.
Step 2: The Signature Removal Test
Delete the signature (everything after the second dot) and send the token back to the server. If the server accepts a token with a missing signature, the backend validation library is catastrophically broken.
Step 3: The Expired Token Test
Wait for the token's exp (expiration) timestamp to pass. Send the expired token to the server. It must result in a strict HTTP 401 Unauthorized error. If it succeeds, the server is failing to validate expiration metadata.
Step 4: Forgery via Algorithm Manipulation
Change the "alg" header to "none". Send the token. Next, attempt the Asymmetric-to-Symmetric confusion attack by forcing the "alg" to "HS256" and signing it with the server's public key. If either succeeds, instantly flag it as a Critical/P1 vulnerability.
Summary
Modern authentication is a massive cryptographic undertaking. Securing it requires extreme precision:
- Enforce PKCE: Never use the outdated Implicit Grant. Always use the Authorization Code Flow with PKCE, enforcing strict
code_verifiervalidation. - Validating the Math: A JWT is only secure if the signature is mathematically validated on every single request. Never trust the payload until the signature is confirmed.
- Prevent Algorithm Confusion: Hardcode the expected algorithm in your backend validation library. Never allow the JWT header to dictate which algorithm the server should use to verify it.
- Store Securely: Never store JWTs in local browser storage. Use
HttpOnlycookies to protect against XSS token harvesting. - Implement DPoP: Evolve beyond basic Bearer tokens by demanding Proof-of-Possession to absolutely neutralize the threat of stolen JWTs.
Conclusion
Stateless authentication using OAuth 2.0 and JWTs allowed the internet to scale to billions of mobile devices and microservices. However, moving the authorization state from the server's secure memory into a client-held plastic keycard introduced an array of new threats. The responsibility of security has shifted from simple database lookups to advanced cryptographic validation. By employing rigorous OAuth JWT testing, security teams can ensure that their applications do not fall victim to signature forgery, algorithm confusion, or token hijacking, keeping the true power of stateless architecture intact and secure.
FAQs
1. Is it safe to put my email address in a JWT payload? Yes, but you must understand that the JWT payload is just Base64Url encoded, it is not encrypted. Anyone who intercepts the token can read your email address. It is "safe" in the sense that they cannot alter your email address without invalidating the mathematical signature at the bottom. Never put highly sensitive data (like a plaintext password or SSN) inside a JWT payload.
2. What is the difference between an Access Token and an ID Token? An Access Token (issued by OAuth 2.0) is used to access an API (e.g., getting permission to read a database). An ID Token (issued by OpenID Connect) is strictly used to verify the identity of the user (e.g., proving the user's name is John). You should never use an ID token to authorize API requests.
3. Why do we need Refresh Tokens? Access tokens should be very short-lived (e.g., 15 minutes) to minimize the damage if they are stolen. A Refresh Token is a long-lived credential used strictly to request a new Access Token in the background, keeping the user logged in without forcing them to type their password every 15 minutes.
4. How do you revoke a stateless JWT?
This is the hardest problem in JWT architecture. Because the server doesn't keep a database of active sessions, it cannot easily "delete" a JWT. You must either wait for the token to naturally expire (the exp claim) or implement a server-side "Blocklist" to track revoked tokens, which unfortunately re-introduces the scalability problem JWTs were designed to solve.
5. How does a hacker steal a JWT?
Primarily through Cross-Site Scripting (XSS) if the token is stored in localStorage. They can also steal it through Man-in-the-Middle (MitM) attacks if the traffic isn't strictly using HTTPS, or by finding an open browser tab on a shared public computer.
6. Can we use symmetric encryption (HS256) for enterprise applications? It is generally discouraged for distributed microservices. HS256 requires that every single microservice validating the token must have a copy of the master secret key. If one minor microservice is breached, the master key is stolen, and the attacker can forge tokens for the entire enterprise. Asymmetric encryption (RS256) allows microservices to verify tokens using only the public key.
7. Should we build our own JWT validation library? Absolutely not. Cryptography is incredibly difficult to implement flawlessly. Always use industry-standard, heavily audited open-source libraries to parse and validate JWT signatures.