Infrastructure Testing Using Terraform
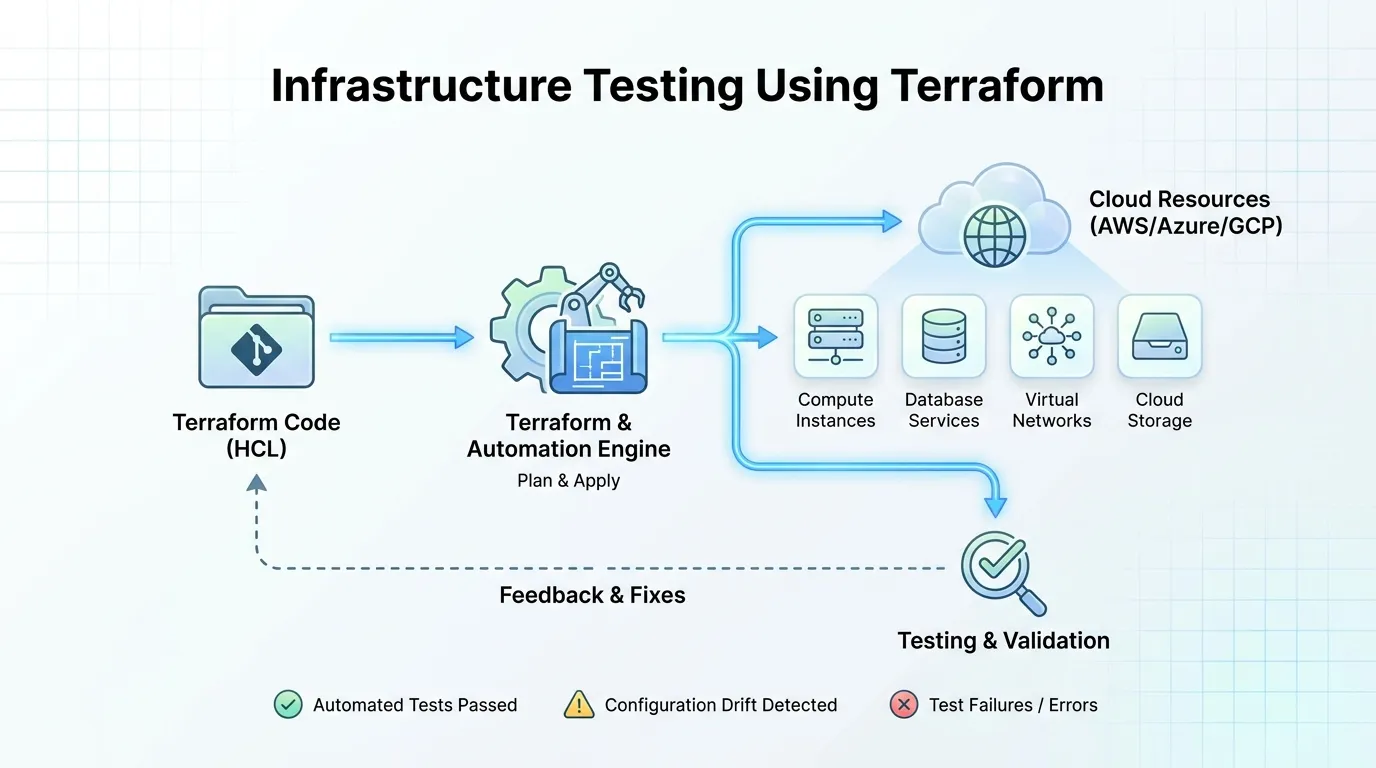
The widespread adoption of cloud computing initiated a fundamental shift in how organizations procure servers, networks, and databases. Hardware was transformed entirely into declarative software lines, birthing the concept of Infrastructure as Code (IaC). Terraform quickly established itself as the global enterprise standard for IaC, allowing engineers to reliably provision incredibly complex, multi-cloud architectures.
However, as organizations began treating their infrastructure exactly like application software, a glaring vulnerability emerged in the developer workflow: testing. While an organization would never dream of deploying Java code without running an extensive suite of unit and integration tests, that same organization frequently deployed massive, thousands-of-lines Terraform modules into production based entirely on manual code reviews. The fallout was inevitable—misconfigured IAM policies, open S3 buckets, and catastrophic cloud outages.
To bridge this crucial gap, DevOps architects are aggressively mandating formalized infrastructure testing using Terraform. In this comprehensive technical guide, we will decompose the evolving ecosystem of static evaluation, continuous compliance testing, runtime validation, and the distinct methodologies shifting the testing of virtual hardware deeply to the left.
The Consequences of Untested Infrastructure
To understand the architecture of modern IaC testing, one must first recognize the consequences of its absence.
Financial Hemorrhaging
If a developer introduces a syntax loophole in an application logic function, it might cause a temporary glitch. If an infrastructure engineer accidentally introduces a loop in a Terraform module that infinitely provisions high-tier AWS EC2 instances, the error quickly manifests as tens of thousands of dollars in wasted cloud computing costs in an hour.
Unseen Security Breaches
Traditional Application Security (AppSec) tools completely ignore configuration files. Therefore, a perfectly secure microservice architecture deployed onto a Terraform-managed network with an accidentally exposed 0.0.0.0/0 ingress rule is immediately exploitable. Untested IaC represents the most devastating security vulnerability in modern DevSecOps, as an infrastructure flaw affects every application hosted within it.
The Testing Pyramid for Terraform
Like application software, Terraform testing is constructed upon an operational pyramid. Teams cannot jump straight into massive integration testing without establishing a rapid static baseline.
1. Static Code Analysis (SAST) and Linting
The first phase of the pipeline never interacts directly with an active cloud provider. It purely analyzes the localized HCL (HashiCorp Configuration Language) files as static text.
- Formatting and Verification: The absolute bare minimum integration is running
terraform fmtto enforce strict indentation and syntax norms, followed byterraform validateto ensure the core interpolations and module references compile successfully without parsing errors. - Security Scanning (Checkov/Tfsec): As soon as the developer commits their code, aggressive third-party static engines analyze the code block. Tools like Checkov cross-reference the Terraform templates against hundreds of pre-configured global compliance benchmarks (like SOC 2 or HIPAA). If a developer writes a block creating an unencrypted AWS RDS database, Checkov instantly blocks the deployment and highlights the specific line number responsible.
2. Unit Testing in IaC
This is the most debated tier in infrastructure. Terraform is inherently a declarative language, not a procedural one, meaning "traditional" unit testing (like mocking specific variables) is complex.
- The Frameworks: Tools like
conftest(using Open Policy Agent Rego language) orterraform test(recently natively integrated into Terraform) are used to assert explicit facts about the code configuration without executing a real deployment. - The Purpose: A unit test might strictly assert that an internal enterprise tagging module successfully attaches a rigid
[CostCenter]and[Environment]tag string to any virtual machine resource generated via the Terraform plan. It tests the logic of the configuration module.
3. Integration Testing (Deployment Validation)
The ultimate validation occurs when the infrastructure is completely built. Integration testing deploys a physical clone of the proposed cloud architecture, tests it vigorously, and systematically tears it down.
- The Power of Terratest: Developed by Gruntwork algorithms, Terratest is written in Go. A Terratest execution actually stands up the Terraform module in a temporary AWS or Azure account. It then runs explicit HTTP requests against the generated Load Balancer IPs or executes SSH commands into the newly booted EC2 boxes. Once the assertions are met, it automatically fires
terraform destroy. This ensures the infrastructure operates exactly as required within a live cloud ecosystem.
Building a CI/CD Pipeline for Infrastructure
Running tests locally is insufficient. A hardened enterprise architecture integrates the entire Terraform testing suite directly into a CI/CD framework (like GitLab CI or GitHub Actions).
Stage 1: The Fast Feedback Loop
The moment a pull request is raised in the Terraform repository, the pipeline fires the static linting (tflint) and security checks (checkov). Because no physical cloud infrastructure is being deployed, this stage executes in under 5 seconds. If the security gate fails, the PR instantly blocks.
Stage 2: The Dry Run and Policy Enforcement
If the linting passes, the pipeline safely authorizes a terraform plan. This command maps the delta between the desired code state and the actual existing cloud state. The pipeline utilizes tools like Open Policy Agent (OPA) to mathematically audit the generated JSON output of the Plan file, ensuring that the explicit changes to be made (e.g., deleting a database table) are formally authorized by enterprise security.
Stage 3: The Ephemeral Execution
Before code is finally merged to the main branch (which triggers a production deployment), an integration job launches Terratest against a dedicated, isolated "Sandbox Cloud Account." The temporary infrastructure operates flawlessly, providing ultimate validation that the Terraform modules will cleanly deploy onto the live production stack without triggering dependency errors.
The Threat of "Drift"
Infrastructure testing does not magically end the moment the code deploys effectively.
Why Infrastructure Drifts
A developer perfectly tests and deploys a Terraform module establishing five security subgroups. A week later, a sysadmin encounters a midnight server outage. They log directly into the AWS manual console GUI, temporarily alter a security subgroup's firewall to allow traffic, fix the issue, and log out—forgetting to correct the firewall. The physical AWS reality is now fundamentally out of sync with the underlying standard Terraform code. This is known as Configuration Drift.
Testing for Reality
Robust DevOps testing establishes "Drift Detection Pipelines." These run on a standard cron schedule (typically every 12 hours). They run terraform plan continuously against active production without applying it. If the pipeline detects that an external entity altered infrastructure variables outside the mandated GitOps infrastructure flow, the system fires High-Priority PagerDuty alerts to flag the unauthorized, untested environment discrepancy.
Summary
The maturation of IaC demands rigorous continuous testing:
- Acknowledge the Risk: Untested Terraform configuration leads directly to colossal financial cloud waste and massive systemic cyber security breaches.
- Leverage Static Gates: Utilize tools like
tflintand Checkov to catch basic resource misconfigurations in the developer's raw code in under five seconds. - Assert Logical Purity: Utilize Open Policy Agent (OPA) and
terraform testto run local unit tests enforcing explicit corporate security tagging and module composition. - Deploy Terratest: Ensure final validation is handled by live integration execution, actively booting, testing, and destroying infrastructure environments before allowing merges.
- Deploy Continuous Enforcement: Schedule automated scheduled pipelines purely dedicated to tracking down manual configuration drift outside the automated workflow.
- Integrate Aggressively: Move away from manual
terraform applyexecutions from local laptops and exclusively route all execution through gated CI/CD platforms mapped with automated validation phases.
Conclusion
The power of Terraform is undeniably absolute—it provides the capability to spin up 5,000 servers across three global continents with a single carriage return. However, absolute power without intelligent guardrails is merely a faster mechanism for causing production destruction. Implementing comprehensive infrastructure testing using Terraform elevates IaC from a glorified scripting process into an enterprise software engineering discipline. By combining near-instantaneous static security gates, deep localized integration pipelines utilizing Terratest, and ruthless continuous drift monitoring, an organization ensures its underlying cloud architecture remains infinitely adaptable, rigorously compliant, and flawlessly stable.
FAQs
1. Is "terraform plan" actually testing?
It is a form of deployment validation check. terraform plan shows exactly what changes will occur if the code executes. While very helpful, developers must integrate tools like OPA against the output plan log to generate an explicit automated test failure based on company policy.
2. What is the difference between Checkov and Terratest? Checkov is a static analysis tool; it reads your code as a raw text string, finding security flaws instantly without talking to AWS. Terratest is dynamic; it actually powers up the cloud infrastructure using your code, tests if it actively operates securely, and then destroys it.
3. Since Terraform is declarative, how do you unit test an assignment block?
Historically, it was difficult. However, HashiCorp recently integrated a native test function using .tftest.hcl files. This allows tests to inject mock variables and specifically assert that internal logic gates module compositions behave precisely as designed, bypassing the heavy requirement of a live physical cloud deployment.
4. Why should we test infrastructure we didn't write (i.e. HashiCorp public modules)? Because you cannot control a public module’s downstream update vulnerabilities. While the core module logic might be solid, your internal developers might pass an wildly insecure overriding variable parameter through it, breaking compliance architectures internally.
5. How does Drift Detection work in Terraform testing?
A scheduled pipeline runs terraform plan. Terraform pulls the real-time cloud provider state. If the real-time state does not perfectly match the localized state file and current code repository, it automatically logs a failure and flags an active discrepancy alert for engineering remediation.
6. Do we have to use Go to use Terratest? Yes, Terratest is heavily built on the Go language architecture. If your DevOps organization primarily utilizes Python, they often transition to alternative testing frameworks or wrap execution pipelines internally inside generic CI/CD Python automation tools.
7. Can we test Terraform output values specifically?
Yes. Integration tests frequently execute the terraform apply, query the resulting output (such as a database URL string), parse that output string via an automated REST payload or curl request, explicitly validating the infrastructure behaves as promised.
8. Is Open Policy Agent (OPA) strictly for Terraform? No, OPA is a generic, cloud-native policy assessment engine executing Rego logic. It validates everything from API payload strings, Kubernetes Pod definitions, and Terraform Plan json payloads natively, scaling across the entire cloud lifecycle.
9. Why do Integration Tests often fail intermittently in cloud deployments? Cloud environments are heavily asynchronous resources. A Terraform command might successfully initialize the AWS S3 creation parameter, but the AWS background processing queue takes 10 seconds to physically authorize the bucket. Your immediate test request tries to hit it, receiving a 404. Robust integration architectures require deep automated retry loops.