API Security Testing: Tools and Techniques
The visual internet—the websites and UI dashboards that humans interact with—now represents a tiny fraction of total global web traffic. Underneath that surface layer lies a massive, invisible engine powering the digital economy: Application Programming Interfaces (APIs). Mobile apps, smart TVs, B2B integrations, and microservices all communicate by firing billions of raw data queries at backend APIs every single second.
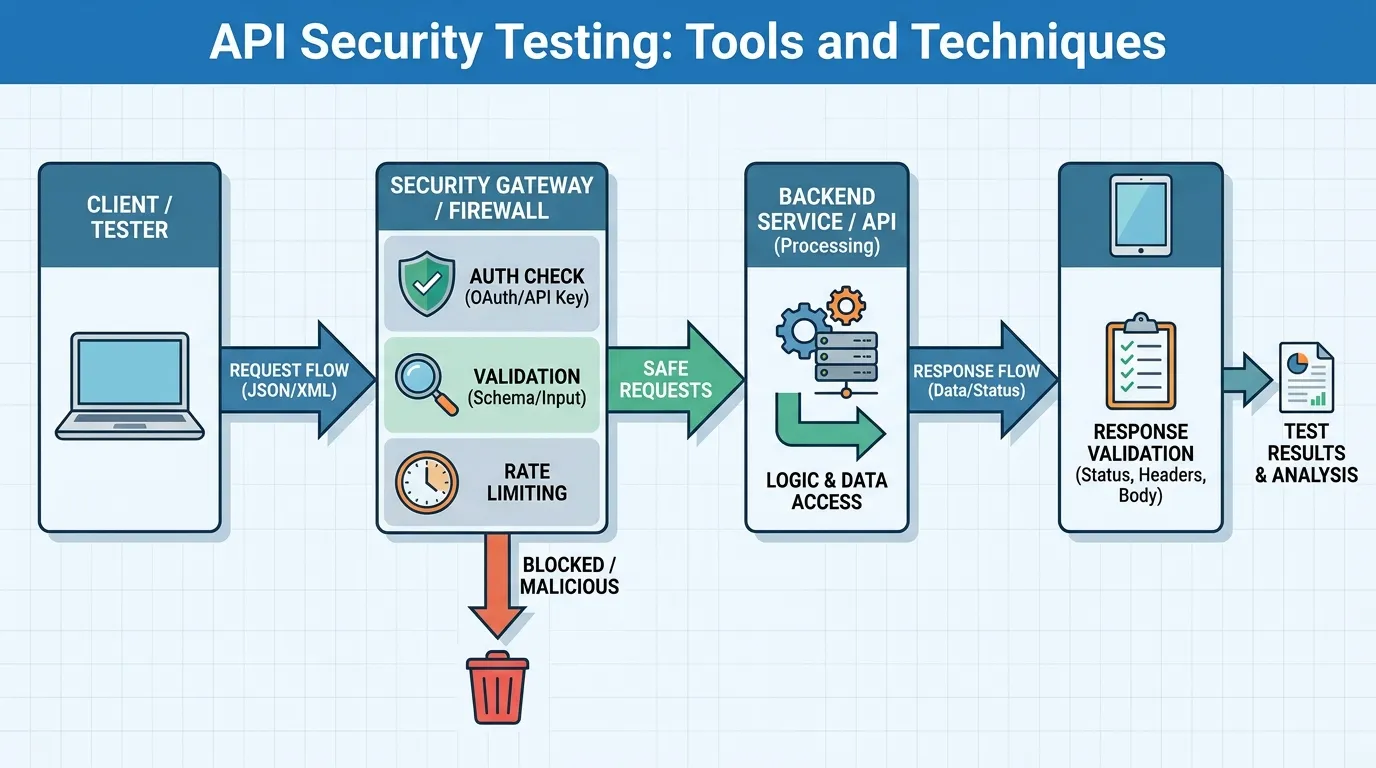
Because APIs deal in raw data rather than HTML, they are the absolute preferred target for modern cybercriminals. An attacker doesn't need to bypass a complex graphical login screen; they simply send a malicious JSON payload directly to a hidden endpoint. As organizations realize that traditional Web Application Firewalls (WAFs) and UI-based vulnerability scanners are entirely blind to these "headless" attacks, API security testing has emerged as a distinct, critical engineering discipline. In this comprehensive 2026 guide, we will explore the plague of BOLA vulnerabilities, the unique dangers of GraphQL, the rise of Machine-to-Machine Authentication, and the automated tools required to secure the modern API gateway.
Why APIs Are the Primary Attack Surface
Testing an API requires a fundamentally different mindset than testing a website.
The Problem of "Shadow APIs"
A developer builds an experimental "v1" API to test a new database feature. Six months later, they launch "v2" and point all customer traffic to it. However, they forget to turn off "v1." That forgotten endpoint is a "Shadow API." It is not monitored by the security team, it lacks modern rate-limiting protections, but it is still physically wired to the production database. API security testing must begin with automated Discovery tools that map the environment to find and kill Shadow APIs before an attacker discovers them.
Data Over-Exposure (Mass Assignment)
APIs are designed for developer velocity, which often leads to over-exposure. Imagine an API endpoint designed to let a user update their profile picture: PUT /api/user/123. A developer might build the endpoint to accept a massive JSON block and lazily update the database with whatever data is provided. An attacker discovers this and sends: {"profile_pic": "new.jpg", "isAdmin": true}. Because the API doesn't validate exactly which fields are allowed to be updated (Mass Assignment), the attacker instantly grants themselves admin privileges.
Defeating BOLA (Broken Object Level Authorization)
If there is one vulnerability that defines the API security crisis, it is BOLA, firmly entrenched at the top of the OWASP API Security Top 10.
The Anatomy of a BOLA Attack
BOLA occurs when an application validates that a user is logged in (Authentication) but fails to validate if the user is allowed to access the specific requested data (Authorization).
- The Legitimate Request: An attacker logs into their bank account and views their own receipt. The bank's mobile app sends this API request:
GET /api/receipts/transaction_id=888 - The Attack: The attacker intercepts that HTTP request using a proxy tool. They change the ID number to someone else's receipt:
GET /api/receipts/transaction_id=889 - The Failure: The API checks the session token, sees the attacker is a valid customer, and returns the data. It fails to check if the attacker actually owns transaction 889.
Testing for BOLA
Standard automated DAST scanners are terrible at finding BOLA. A scanner doesn't know what "ownership" means. Finding BOLA requires complex, authenticated testing. A tester must create two distinct user accounts (User A and User B). They log in as User A, extract User A's private resource IDs, and then aggressively attempt to request those exact IDs using User B's authentication tokens to see if the server leaks the data across the authorization boundary.
The Unique Security Challenges of GraphQL
While REST APIs rely on rigid, predefined endpoints, GraphQL APIs empower the frontend client to ask for exactly the data it wants in a single, deeply nested query. This flexibility is a nightmare for security testing.
- Introspection: GraphQL has a built-in feature called Introspection, which allows a developer to ask the API to return its entire schema (a map of every single possible query and data type). If this is left enabled in production, an attacker can download the entire blueprint of your database in one click.
- Query Complexity (DoS): Because the client dictates the payload, an attacker can write an infinitely nested, recursive GraphQL query (e.g., asking for an Author, their Books, the Readers of those Books, their Favorite Authors, their Books...). Testing must ensure the API enforces strict "Query Depth Constraints" and "Timeouts" to prevent an attacker from intentionally crashing the backend database with a single heavy query.
Machine-to-Machine (M2M) Authentication
As of 2026, the rise of AI agents and autonomous microservices has brought Machine-to-Machine (M2M) API security to the forefront. When a human logs into an API, they use a password or biometric scan. But when the billing microservice needs to talk to the email microservice, how do they securely authenticate?
- Mutual TLS (mTLS): In zero trust environments, testing must validate that APIs require mTLS. This means both the client (the billing service) and the server (the email service) present cryptographic certificates to prove their identity before a single byte of data is exchanged. Testing verifies that API endpoints entirely reject standard HTTP traffic or unauthorized certificates.
- Service Accounts and Scopes: M2M APIs usually authenticate using the OAuth 2.0 Client Credentials flow. Security testing focuses on scoping. If the email microservice is compromised, it should only possess a token with the specific scope to "send email." Testing must prove that the email microservice's token cannot be used to forcefully execute a "refund payment" query against the billing API.
Shifting Left: Schema Validation and Contract Testing
To secure APIs at scale, organizations cannot wait until the API is in production to test it. They must "Shift Left" and test the architectural blueprint itself.
In modern development, an API is usually defined by an OpenAPI Specification (formerly Swagger) file. This YAML/JSON file strictly declares the available endpoints, the required data types, and the authentication requirements. Contract Testing involves integrating a tool directly into the CI/CD pipeline to validate that the actual code matches the OpenAPI "Contract."
- Preventing Data Leaks: If the OpenAPI contract states that the
/usersendpoint should only return thenameandemailattributes, but a developer writes code that accidentally includes thesocial_security_numberin the JSON response, the automated Contract Test will detect the discrepancy and instantly fail the CI/CD build before the code ever reaches production.
Leading API Security Testing Platforms
General-purpose DAST tools struggle heavily with APIs because they are designed to click buttons on a webpage, not parse complex YAML schemas. The industry has responded with dedicated, API-first testing platforms.
1. Salt Security
Salt relies heavily on big data and artificial intelligence to map the API attack surface. It ingests massive amounts of raw, live production traffic to build a dynamic baseline of "normal" API behavior. If an attacker initiates a slow, low-volume reconnaissance attack to map hidden endpoints—a technique that bypasses standard rate-limiting easily—Salt's AI detects the behavioral anomaly and blocks the actor, making it exceptional for runtime BOLA protection.
2. Levo.ai
Levo is an incredible platform focused heavily on the developer and the "Shift-Left" philosophy. It sits inside the CI/CD pipeline and automatically discovers all APIs within the source code. More importantly, it automatically generates thousands of highly customized, dynamic security test cases (fuzzing payloads) based specifically on the business logic it uncovers in the OpenAPI schemas, dramatically reducing the manual scripting burden on security engineers.
3. StackHawk
Built almost exclusively for developers, StackHawk excels at modern DevSecOps integration. It runs seamlessly as a Docker container within a GitHub Action. Developers feed their OpenAPI spec into StackHawk, and it bombards the local API endpoints with specialized tests (like testing for missing JWT signatures or HTTP Verb Tampering) every time the developer pushes a code commit.
Step-by-Step: Securing an Enterprise API Architecture
A mature API testing strategy must encompass the entire lifecycle from code to cloud.
Step 1: Automated Discovery (Curing Context Blindness)
Before writing a single test, deploy a continuous discovery tool. You must maintain a real-time, automated inventory of every single API endpoint in your environment, including legacy V1 APIs and undocumented microservices.
Step 2: Schema-Driven DAST Testing
In the CI/CD pipeline, mandate that every API must have an OpenAPI schema. Feed that schema into an API-specific DAST tool (like StackHawk) to run a barrage of automated authentication bypass and payload fuzzing tests on every pull request.
Step 3: Complex BOLA Testing
Utilize advanced platforms (or expert manual testers using proxy tools) to specifically write test cases for Broken Object Level Authorization. Ensure that your authorization checks are enforced inside the core application logic, not just at the API Gateway layer.
Step 4: Continuous Runtime Shielding
Deploy a dynamic API Security Posture Management tool (like Salt Security) to monitor live traffic. Protect the endpoints against slow-drip scraping attacks, query-depth Denial of Service (DoS) attacks on GraphQL, credential stuffing, and unauthorized M2M lateral logic execution.
Summary
APIs are the nervous system of the modern enterprise, and protecting them requires specialized approaches:
- Acknowledge the Shift: Traditional Web Application Firewalls (WAFs) cannot protect APIs from complex logic attacks. You need API-specific security tooling.
- BOLA is King: Broken Object Level Authorization is the most devastating API flaw. Test rigorously to ensure users can only access their own data.
- Lock Down GraphQL: GraphQL is incredibly powerful but inherently dangerous if unchecked. Always disable introspection in production and strictly limit query complexity.
- Secure Machine Identities: Treat your internal microservices as untrustworthy actors. Force them to use strict, scoped M2M authentication and Mutual TLS.
- Shift Left with OpenAPI: Use your OpenAPI specifications to run automated Contract Tests in the CI/CD pipeline, catching structural flaws before they compile.
- Eliminate Shadow APIs: You cannot secure what you cannot see. Use continuous discovery tools to map every forgotten or undocumented endpoint in your cloud.
Conclusion
The era of security through obscurity is over. You can no longer hide a vulnerable endpoint and hope an attacker simply doesn't "click the right button" on your website. Modern attackers use automated scripts to map your entire API landscape in milliseconds. By adopting a "Shift-Left" mentality, enforcing strict schema contracts, auditing the interactions between non-human machines, and deploying intelligent API security testing platforms capable of understanding complex business logic, engineering organizations can protect their most vital data pipelines and safely scale their microservices architecture.
FAQs
1. Is a REST API inherently safer than a GraphQL API?
Not necessarily safer, but fundamentally simpler to secure. REST endpoints are highly predictable, meaning traditional firewalls can easily understand them. GraphQL uses a single endpoint (/graphql) to process infinite variations of queries, meaning security checks must be written deeply into the custom application code.
2. What is a "Zombie API"? While a "Shadow API" is an API the security team was never told about, a "Zombie API" is an outdated, depreciated API version (like v1) that was supposed to be turned off but was accidentally left running. Attackers love Zombie APIs because they usually lack the security patches applied to the newest versions.
3. Does implementing OAuth 2.0 protect against BOLA? No. OAuth 2.0 handles Authentication and basic Delegation. It proves the user is logged in. BOLA is an Authorization failure. Even with a perfect OAuth 2.0 token, if the API doesn't check if the user owns the specific database record they are requesting, BOLA still occurs.
4. Can we use Burp Suite to test APIs? Absolutely. Burp Suite Professional is an incredible tool for manual API testing. Testers intercept the raw JSON requests and manually alter parameter IDs to hunt for BOLA vulnerabilities. There are also powerful Burp extensions specifically designed to automatically parse and test OpenAPI schemas.
5. How do attackers discover hidden APIs? They often don't have to guess. They download the company's Android or iOS mobile application, decompile the code, and extract the hardcoded API URLs that the mobile app uses to communicate with the company's backend servers.
6. What is API Rate Limiting, and why does it matter? Rate limiting restricts how many times a user can hit an API within a minute. Without rate limiting, an attacker can launch a script that attempts 10,000 different passwords per second (Credential Stuffing) or sequentially requests every single user ID in the database from 1 to 10,000 (Data Scraping).
7. Who is responsible for API security? In 2026, it is a DevSecOps responsibility. Developers must write secure schemas and write explicit authorization checks in their code. Security engineers provide the guardrails, discovery tools, and runtime monitoring to ensure those practices are enforced at scale.
8. What exactly is a BFLA vulnerability?
Broken Function Level Authorization (BFLA) is related to BOLA, but instead of accessing objects, the attacker accesses administrative functions. For example, a low-level user sending a DELETE /api/users/4 request. If the API fails to verify that the user's role is "Admin", the deletion succeeds, triggering an exploit.
9. How do we test for Insecure Direct Object References (IDOR)? IDOR is essentially the older, web-app term for BOLA. Testing involves creating multiple accounts at different privilege tiers, extracting the unique identifiers (like user IDs or document IDs) from a high-privilege account, and then intentionally injecting those IDs into the API requests of the low-privilege account to see if the server blindly fulfills the request.