Introduction
In the world of cybersecurity, there are two ways to find out if your systems are vulnerable. You can wait for a real hacker to find the holes, or you can find them yourself. The second option is known as Vulnerability Assessment and Penetration Testing (VAPT).
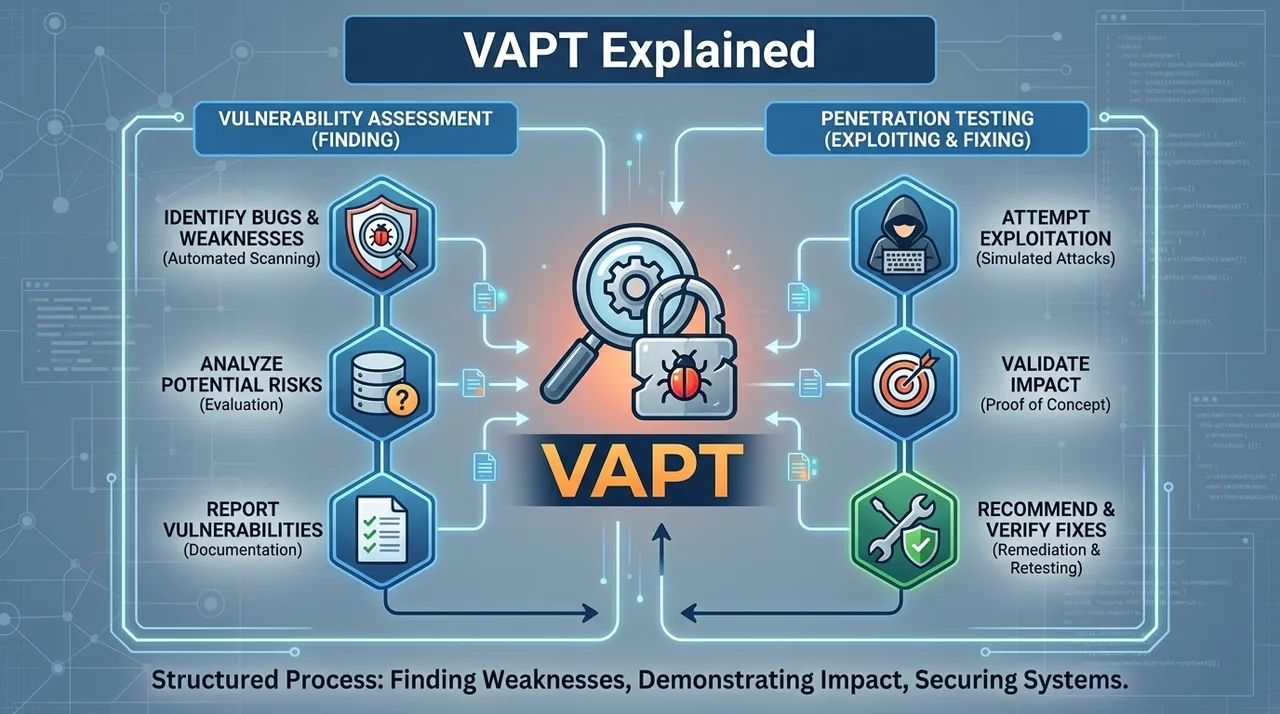
VAPT is a unified security testing approach that combines two distinct but complementary methods. The "Vulnerability Assessment" part is a broad scan that identifies potential weaknesses, while the "Penetration Testing" part is a deep-dive attempt to exploit those weaknesses to see how far an attacker could get.
Understanding vapt security is critical for any organization that wants to move beyond "Reactive" security and enter the realm of "Proactive" defense. In 2026, VAPT is no longer a luxury for big banks; it is a standard business requirement for any company that handles customer data or operates in the cloud.
In this guide, we will explore:
- The Core Components: VA vs. PT
- The VAPT Lifecycle: How a Professional Test is Conducted
- Different Types of VAPT: Network, Web, and Mobile
- The Deliverable: Understanding the VAPT Report
- Best Practices for Frequency and Vendor Selection
The Two Halves of VAPT
While often spoken of together, VA and PT are very different activities with different goals.
Vulnerability Assessment (VA)
A VA is a "horizontal" scan. It uses automated tools (like Nessus or Qualys) to look for thousands of known vulnerabilities across your entire network. It provides a broad list of "what is broken."
- Goal: Comprehensive visibility.
- Outcome: A prioritized list of vulnerabilities (High, Medium, Low).
Penetration Testing (PT)
A PT is a "vertical" attack. An "Ethical Hacker" (the pen tester) takes one of the vulnerabilities found during the VA and tries to use it to "break into" the system. They might use it to steal data, gain administrative control, or "move laterally" across the network.
- Goal: Real-world risk validation.
- Outcome: Proof that a vulnerability can be exploited and what the business impact would be.
The VAPT Lifecycle: The Ethical Hacker's Roadmap
Professional testing follows a strict, repeatable methodology to ensure accuracy and safety.
1. Scoping and Planning
The most important step. The organization and the tester define exactly which systems are "In Scope" and which are "Off Limits." You don't want a pen tester accidentally taking down your production database during peak business hours.
2. Information Gathering (Reconnaissance)
The tester gathers as much data as possible about the target. This includes IP addresses, domain names, employee names, and the versions of software the company is running. In 2026, this stage often includes "Passive OSINT" (Open Source Intelligence) gathering from social media.
3. Vulnerability Detection (Scanning)
The tester runs the automated VA tools to find the low-hanging fruit—the unpatched systems, the default passwords, and the misconfigured firewalls.
4. Exploitation
This is where the "Penetration" happens. The tester uses manual and automated techniques to bypass security controls. The goal is to gain a foothold and demonstrate the potential for data theft or system takeover.
5. Reporting and Remediation
The final product is a detailed report that outlines exactly what was found, how it was exploited, and most importantly, how to fix it.
Types of VAPT Services
Testing can be focused on different areas of your digital infrastructure.
Network VAPT
Focuses on the "pipes" and "servers." It looks for weaknesses in your VPNs, firewalls, and internal servers. It is the most common form of security testing.
Web Application VAPT
Focuses on the code. It looks for "OWASP Top 10" vulnerabilities like SQL Injection or Cross-Site Scripting (XSS). In 2026, this is critical for any company that hosts an online portal or a SaaS platform.
Mobile and Cloud VAPT
Focuses on the unique risks of iOS/Android apps and cloud environments (AWS, Azure). These tests look for insecure API calls, misconfigured cloud storage "buckets," and poor identity management.
VAPT for the Internet of Things (IoT): A Specialized Challenge
Standard web and network VAPT tools often fail when testing IoT devices (smart cameras, industrial sensors, medical devices).
Hardware and Firmware Analysis
In an IoT VAPT, the tester doesn't just look at the network traffic. They might physically disassemble the device to find "UART" or "JTAG" ports that allow them to extract the Firmware. They then reverse-engineer that firmware to find hardcoded passwords or hidden backdoors.
Protocol Fuzzing
IoT devices often use specialized protocols like MQTT, Zigbee, or LoRaWAN. A specialized VAPT tester will perform "Fuzzing" — sending millions of slightly malformed packets to the device to see if it crashes or reveals a vulnerability. In 2026, as our homes and cities become "Smarter," IoT VAPT is becoming the most critical form of proactive defense.
Automated vs. Manual Penetration Testing
A common misconception in vapt security is that a "Penetration Test" can be fully automated. While automation is great for the Assessment phase, the Testing phase requires human intuition.
The Limits of Automation
Automated scanners are excellent at finding known vulnerabilities (like a missing security patch). However, they are "blind" to business logic flaws. For example, a scanner won't know that a normal user shouldn't be able to change the price of an item in a shopping cart by modifying the URL. Only a human manual tester can understand the "context" of an application and find creative ways to abuse it.
The Balanced Approach
In 2026, the gold standard is a "Hybrid VAPT." Automation handles the 99% of common, repetitive vulnerabilities, allowing the human ethical hacker to spend their expensive time on the 1% of sophisticated, high-impact flaws that could actually lead to a major breach.
The Critical Need for Post-Remediation Testing
The single biggest mistake organizations make after a VAPT is fixing the holes and then assuming they are safe.
Verifying the Fix
Many "fixes" actually break something else or, worse, don't actually fix the root cause. For example, if a tester finds a SQL Injection vulnerability, the developer might simply "blacklist" certain characters like a single quote ('). A creative attacker will quickly find a way around this blacklist. Post-remediation testing (also known as a "Re-scan") is where the original tester goes back and tries to break in using the exact same methods as before. Only when the tester confirms the hole is closed should the vulnerability be marked as "Resolved."
The Future of Pen Testing: AI vs. AI in the 2026 Sandbox
The most advanced VAPT firms are now using "Defensive AI" to test "Offensive AI."
The Autonomous Sandbox
Instead of a human manually typing exploits, they deploy an Autonomous Pentesting Agent into a safe "Digital Twin" of the client's network. This agent uses reinforcement learning to find thousands of attack paths in seconds. The human tester then reviews these paths to see which ones are the most likely to be used by a real-world adversary. This allows for "Exhaustive Testing" that was physically impossible for human teams to perform in the past.
Case Study: The Logic Bomb That Scanners Missed
In 2025, a major healthcare provider had their patient portal scanned by three different automated vulnerability scanners. All three scanners gave the portal a "Clean" bill of health.
However, during a manual VAPT, a human tester noticed a flaw in the "Password Reset" logic. By intercepting the password reset request and changing the "User_ID" parameter to a different number, the tester was able to reset the password of any patient in the database.
Because the web server was technically functioning correctly and no "malicious code" was being sent, the automated scanners saw nothing wrong. It was a failure of logic, not a failure of software. The manual VAPT identified this critical flaw in 4 hours, preventing what would have been a catastrophic HIPAA violation and a massive PR disaster.
Conclusion
VAPT is the ultimate "reality check" for your security team. This vapt security guide highlights that while tools are important, the human creativity of the pen tester is what identifies the most dangerous threats.
In 2026, as threats become more automated, the frequency of testing must increase. Organizations are moving toward "Continuous VAPT" models, where testing happens every month rather than every year. By identifying and fixing your weaknesses before the criminals do, you can ensure that your organization remains a "Hard Target" in an increasingly dangerous digital world.
VAPT vs. Bug Bounty Programs
In 2026, many organizations use both. While VAPT is a "point-in-time" professional audit, a Bug Bounty is an ongoing "continuous" test by thousands of independent researchers. VAPT provides the Assurance that you have met a specific standard, while Bug Bounties provide the Discovery of the weird, edge-case bugs that even the best professional labs might miss.
Frequently Asked Questions
When performed by professionals (like CREST or OSCP certified testers), VAPT is extremely safe. The "Scoping" phase ensures that any high-risk tests are performed against a "staging" environment or during maintenance windows. Professional testers use "non-destructive" exploits that provide "Proof of Concept" without causing downtime.